State of Phishing with MITRE ATT&CK
September 21, 2022 by Kimberly Reali and Justin Lopez

What is Phishing?
Phishing attacks are the widespread practice of tricking users into providing sensitive information or performing an action that helps the attacker gain access to your network. This technique is the most common attack today because it is cheap, fast, and effective. No matter how often users are warned not to click on untrusted links, there are still those who let their guard down for just a second, and that’s all it takes.
Since 1995, phishing attacks have become far more advanced than just obtaining credentials or sensitive information, or tricking individuals into sending money. Now attackers use artificial intelligence (AI) and Machine Learning (ML) to mimic high ranking officers of a targeted organization. The traditional mitigation efforts revolve around Indicators of Compromise (IOC), like hash values, IP addresses, and domains, that adversaries can easily change in order to work around defenses and continue the attack before the defender can react. But now there’s a tool available that makes it harder for adversaries to work around defenses and forces them to change their entire behavior, allowing defenders to learn enough about the attack to get ahead of them and stop it!
State of Phishing
Now with the advances of technology, attackers have turned to artificial intelligence such as DeepFake, a tool that can recreate or replace voices and media with the intention to impersonate someone else which makes phishing attacks harder to mitigate against. KnowBe4, a leader in security awareness and training, reported that “91% of all successful data breaches started with a spear phishing attack.”
On March 10, 2022, the FBI Cyber Division released a warning about the increase of “synthetic content” that they defined as a “generated or manipulated digital content, which includes images, video, audio, and text”, otherwise known as DeepFake using Artificial Intelligence (AI) and Machine Learning (ML). Phishing, once an inexpensive effort that required minimal effort, has now become more expensive – but more financially rewarding – with the advancement of AI and ML.
Research shows that a convincing cloned voice can be developed with just a few seconds of sample audio. Distinguishable personal voice traits, such as pronunciation, tempo, intonation, pitch, and resonance -- necessary items to create a convincing DeepFake -- are likely to be present to feed into the machine learning algorithms. However, the more source audio and training samples, the more convincing the output was. With all this new technology helping adversaries create new attack vectors, and with new threat groups entering the cyber threat arena with multiple names, how do we keep up and get ahead of them?
If only there was a tool that could compare the behaviors of an attack against all globally known attacks, predict what it will likely do next, expose the likely attacker behind it, and provide mitigation methods to prevent it.
The MITRE ATT&CK® Framework
MITRE ATT&CK Framework is a free and open-source repository containing a break-down and classification of real-world cybersecurity attack behaviors, analytics and Cyber Threat Intelligence (CTI) collected from a rapidly growing cybersecurity community since 2013. The MITRE ATT&CK Framework has become widely known as the de facto standard for understanding the behaviors and techniques used by advanced persistent threat (APT) groups through the entire lifecycle of the attack.
The ATT&CK behaviors are divided into three (3) categories: Tactics (Why the attacker is performing an action), Techniques (How the attacker will achieve their tactical goal) and Procedures (Specific instance of how a Technique is used). These are known as TTPs. There are 14 Tactics listed across the top of the ATT&CK Matrix and 577 techniques and sub-techniques that have been used by threat groups listed under each Tactic. Tactics and Techniques are each given a unique ID (TA#### = Tactic and T#### = Technique) For example: The Technique of Phishing is tagged with the ID [T1566].
ATT&CK’s Cyber Threat Intelligence (CTI) is a cluster of profiles for 134 Threat Groups (Also represented by a unique ID “G####”) based on real world attacks that combine the TTPs they’ve used, industries they’ve targeted, and software/tools they’ve used in their attacks to provide a full profile of the attack. This profile can be use with automated systems to create actionable intel for alerting, and can be mapped to the Tactic and Technique IDs used across all industries.
Phishing Attacks Using MITRE ATT&CK Framework [non-technical]
As a user, you are the number one layer of security against cyberattacks. The best thing you can do as a user to protect your company’s sensitive information is to first, be aware of your company’s Security Policies and Procedures. If you suspect a DeepFake or phishing attempt (via email, VOIP, video conference or even streaming video), notify your Help Desk or Security Department. If your Security Policy allows, you can hover or right click on a link then "Copy web address” into a free online tool like Urlscan.io, CheckPhish, or VirusTotal. Never paste the URL directly in your browser!
The second-best thing you can do is to be aware of current phishing campaigns that are a threat to your industry and the techniques used to fool users into clicking a link or opening a document attached to the email (Ex. Deepfakes are currently being used by attackers to apply for remote IT job positions). MITRE ATT&CK provides some real-world attack scenarios for spear phishing attachments [T1566.001], spear phishing links [T1566.002] and spear phishing via 3rd party services [T1566.003] (Ex. social media, personal webmail and deepfake streaming media).
And third, users should adopt a “Zero Trust” approach to all correspondence, including those from trusted sources. Being cautious, vigilant, and attentive will go a long way in securing your organization’s data and protecting it from ransomware.
Phishing Attacks Using MITRE ATT&CK Framework [technical]
One of the most important things you can do as a CISO, System Engineer or IT Security Manager is to create Security Policies that are based on your risk assessments. As mentioned earlier, “91% of all successful data breaches started with a spear phishing attack.” The Cybersecurity and Infrastructure Agency (CISA) released Alert (AA22-137A) in May 2022 listing “Phishing [T1566]” as one of the top 5 “Weak Security Controls and Practices Routinely Exploited for Initial Access”. MITRE ATT&CK offers a wealth of information shared among the cybersecurity community about real-world scenarios and offers proven ways to detect and mitigate against phishing attacks.
A good starting place is MITRE Engenuity's Center for Threat Informed Defense (CTID) “Top 10 Techniques” calculator to identify the techniques that are the highest risk for your company/organization.
Once you identify the behaviors of the attack, you can identify which techniques translate to each behavior and map the behaviors to the tactics under each technique.
A phishing attack may look like this after mapped:
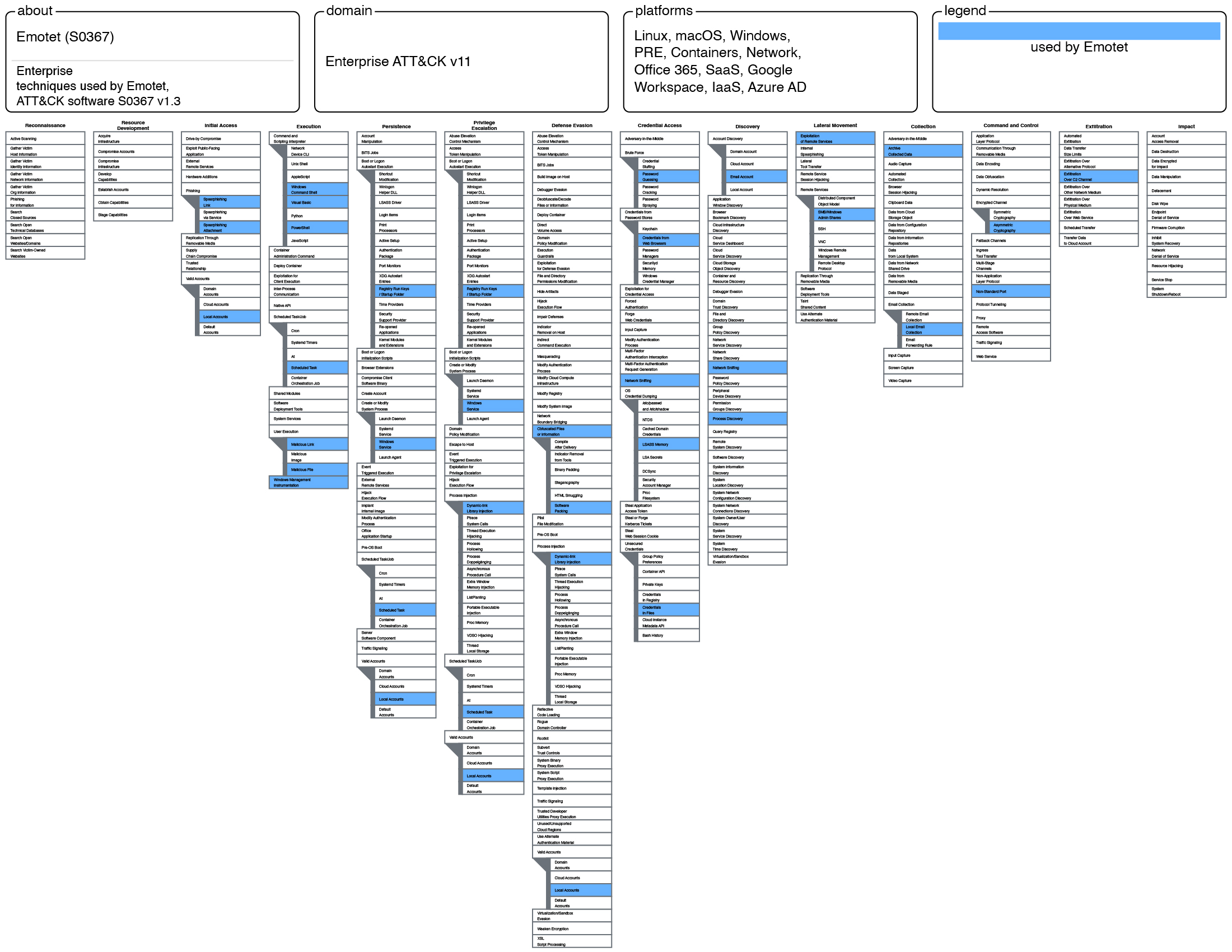
Once mapping of ATT&CK behaviors are complete, you can download the mapping in JSON, Excel or .SVG formats. Mapping IDs is how ATT&CK associates Threat Groups [G####] that target your industry, what TTPs ([TA####] [T####]) they have used, and what software [S####] they’ve used in previous attacks. This knowledgebase with the top 10 techniques calculator provides you with actionable intelligence to assess what Techniques may be your biggest risk, so you can now predict and protect against them. ATT&CK collects intelligence on the Data Sources [D####] to monitor for detection and the Mitigations [M####] that will prevent a specific technique from successfully executing.
MITRE ATT&CK recommends a few ways to detect spear phishing attachments, spear phishing links and spear phishing via service: monitor third-party application logs, new file creations on endpoints, unusual use of protocols in network traffic, monitor email header for spoofed email senders and monitor new and unusual network data flows.
Historically, cybersecurity teams have only had indicators of compromise (IOC) to indicate an attack using IPs, hostnames, domain names, hashes, etc. But these indicators can be altered and changed by attackers quickly and easily to hide from security controls. MITRE ATT&CK’s threat-informed approach gets ahead of the attackers. It is significantly harder for an adversary to change the behavior (TTPs), and gives you more time to mitigate against it – a window of time that wasn’t available before.
There are several mitigations for Phishing [T1566]. Examples include antivirus on the endpoint [M1049], restrict access to web content not ‘necessary’ for operations (Ex. social media platforms, personal webmail, etc.) [M1021], user AD account management to limit user ability to consent to unauthorized 3rd party applications [M1018], and Multifactor Authentication [M1032].
One of the most important mitigations to implement is a companywide Security Awareness Training Program and conduct periodic simulations using the guidelines provided by NIST Special Publication 800-50 (Building an Information Technology Security Awareness and Training Program) and the Security Policies you already have in place.[1] A successful program is both engaging and relevant to your company/industry and meets compliance requirements. If you already have a program in place, ask yourself, “Is it changing the behaviors of users?” MITRE ATT&CK has mapped user training to as many as 40 threats to an organization. Users can be empowered with this knowledge and become an invaluable first line of defense for your organization.
Another initiative of MITRE ATT&CK is The Common Attack Pattern Enumeration and Classification (CAPEC™), a catalog of known attack patterns seen in the wild. It was established by the U.S. Department of Homeland Security to help industries build more secure “cyber-enabled” security controls, including valuable information about Phishing.
Sharing information and collaboration from everyone in the cybersecurity community[2] is the backbone of MITRE ATT&CK’s architecture and is used by all industries across the world. Thanks to MITRE ATT&CK’s extensive collaboration with the cybersecurity intelligence community and local and federal government agencies to build this behavioral-based threat model knowledgebase, we now have the tools that can help prevent your business/industry from becoming another statistic on the long list of cyber-attack victims.
“We have no owners or shareholders, and we don't compete with industry. This lack of commercial conflicts of interest forms the basis for our objectivity.” -MITRE
[1] NIST SP 800-50 Rev. 1 ‘Building an Information Technology Security Awareness and Training Program’ is currently in Pre-draft phase and scheduled to be released in early 2022.
[2] Vendors, researchers, analysts, other countries, U.S. Department of Homeland Security military, OWASP, CWE, etc.